
Best-Fit vs PHP CGI
It might be consider boring that yet another vulnerability has been found in PHP. It’s more than obvious that it’s majority of the IT staff right now:
But this time I’ve decided to mention about that flaw due to it’s simplicity. DEVCORE team have discovered a remote code execution vulnerability in PHP and classified it as critical. Path has been released on 6th June 2024.
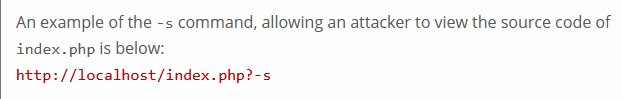
Best-Fit as encoding conversion feature in Windows OS had it’s prime in 2012 before CVE-2012-1823 has been released, when attacker were able to disclose source code and obtain arbitrary code execution by simply passing one of the parameter in URL:
Until now this vulnerability was considered dead, but hey, it would be boring for such a long time, right?
Basically, mentioned patch was advising to configure your web server to not let these types of requests with query strings starting with a ”-” and not containing a ”=” through. Adding a rule like this should not break any sites. Eventually, it looks like due to Traditional Chinese, Simplified Chinese, or Japanese encoding technique, rules were not able to detect that parameter when CGI mode was enabled..
Recall, retreat, repeat ~Windows
Alright folks, buckle up because we’re diving into a saga straight out of the tech world that’s equal parts fascinating and eyebrow-raising.
Microsoft’s AI Tool Recall: Big Brother or Best Buddy?
So, here’s the deal: Microsoft decided their AI tool, Recall—which takes a screenshot every few seconds—won’t be running automatically on their Copilot+ computers. They’ve also thrown in some extra security measures to make life harder for hackers. Because, you know, hackers have it too easy already, right?
Recall was introduced by Microsoft on May 20, and the cybersecurity community collectively had a heart attack. They labeled it a “privacy nightmare” and a “goldmine for hackers.” Can’t imagine why. I mean, who wouldn’t want their computer acting like a nosy paparazzo?
So, what’s the fuss all about? Microsoft’s Copilot+ computers come equipped with this Recall feature. It’s an AI tool with a “photographic memory” that snaps a screenshot every 5 seconds while you’re using your computer. The idea is to help users quickly find information. Picture this: Recall has access to all your files, photos, emails, and search results. Yeah, sounds totally safe and not creepy at all.
Microsoft assured us that the data is stored locally and is securely encrypted, and only people with physical access to the computer can get to Recall. Sounds comforting, right? Not so much.
Cybersecurity experts weren’t buying it. They warned that Recall is a massive privacy risk and a juicy target for hackers. To make things even more interesting, cybersecurity pro Kevin Beaumont discovered that this AI feature stores data as plain text. Yep, you heard that right—plain, old, easily hackable text. It’s like leaving your diary open in a coffee shop.
According to The Verge, a bunch of tools for stealing Recall data have popped up recently. Cue the dramatic music.
On June 7, Microsoft responded to the backlash and updated their blog with changes to Recall. Here’s the scoop: the AI tool will now be turned off by default. If you want to use it, you’ll need to flip a switch in the settings. Easy peasy, right?
But wait, there’s more! To use Recall, you’ll also need to register with Windows Hello. That’s Microsoft’s fancy login system using facial recognition, fingerprints, or a PIN. Because nothing says secure like letting your computer scan your face every time you log in.
Microsoft also mentioned beefing up data protection with additional encryption:
“We’re adding extra layers of data protection, including ‘just in time’ decryption, safeguarded by Windows Hello Enhanced Sign-in Security (ESS). Recall screenshots will only be decrypted and accessible when the user is authenticated. Plus, we’ve encrypted the search indexes,” wrote Pavan Davuluri on the Microsoft blog.
Microsoft managed to roll out the Recall update just in time before the Copilot+ computers hit the market on June 18. Talk about cutting it close.
So there you have it, folks. Microsoft’s Recall tool: a tech marvel or a privacy debacle? Only time will tell. But for now, remember to smile—you never know when your computer might be taking a screenshot.
Sources: https://arstechnica.com/ai/2024/06/windows-recall-demands-an-extraordinary-level-of-trust-that-microsoft-hasnt-earned/ https://www.darkreading.com/application-security/microsoft-modifies-recall-ai-feature-privacy-security-failings https://www.wired.com/story/microsoft-recall-off-default-security-concerns/
Euro 2024 - cyber game
Euro 2024: Cybersecurity Kicks into High Gear
With the UEFA European Football Championship kicking off on June 14 in Germany, the local police are on high alert. And they’re not just watching out for the usual suspects like hooligans and terrorists. Nope, they’re also keeping a close eye on the digital battlefield.
Thousands of fans are flocking to the Elbe and Rhine rivers to cheer for their favorite teams until mid-July. But it’s not just the fans who are pouring in. Germany’s Interior Minister, Nancy Faeser, has rolled out the red carpet for about 350 foreign police officers to assist during the tournament. Talk about international cooperation!
Faeser made it clear that “propaganda and hate speech will not be tolerated in Germany.” She also highlighted the range of threats under scrutiny: terrorism, hooliganism, everyday crimes, and—you guessed it—cyberattacks.
A Nod to the Past: Remembering Olympic Destroyer
Now, why is this such a big deal? Cast your minds back to the Olympic Destroyer cyberattack during the 2018 Winter Olympics in Pyeongchang. That cyber offensive disrupted IT systems, took down Wi-Fi, and caused all sorts of digital mayhem. It was a stark reminder that major sporting events are prime targets for cybercriminals.
With that in mind, German authorities are pulling out all the stops to prevent a repeat scenario. They’ve learned from past incidents and are ramping up their cybersecurity measures. And it’s not just about stopping hackers; it’s also about countering misinformation.
Cyberattacks and Disinformation: A One-Two Punch
In recent weeks, Europe has seen a surge in cyberattacks, and Poland’s Press Agency was among the victims. Cybercriminals are increasingly targeting major events to spread chaos and misinformation. With the Olympics in Paris and Euro 2024 in Germany, the stakes are higher than ever.
Misinformation is a particularly insidious threat. During high-profile events like the Euros, false narratives can spread like wildfire, causing confusion and panic. Authorities are on high alert to nip these disinformation campaigns in the bud.
So, while the players are battling it out on the pitch, a different kind of battle is unfolding behind the scenes. Germany is determined to keep the cyber peace, ensuring that the focus remains on the beautiful game—and not on digital disruptions.
Stay tuned and stay secure, folks. Euro 2024 is set to be a thrilling tournament, both on and off the field.
PAP - mystery resolved
In the wake of a cyberattack on the Polish Press Agency (PAP), Deputy Prime Minister and Minister of Digital Affairs Krzysztof Gawkowski assured everyone on Saturday that measures have been put in place to prevent such incidents in the future. According to Gawkowski, PAP is now secure after Friday’s cyber intrusion.
So, what went down? On Friday, the Daily News Service of PAP published a false report about a supposed mobilization in Poland—twice! PAP wasn’t the source of this bogus news. It wasn’t created or sent by any of their staff and was promptly retracted from the service.
“We’ve got our first confirmed details about how the attack on PAP happened,” Gawkowski explained. “It was a well-planned, long-term operation using malware. This malicious software infiltrated one of PAP’s employee accounts, aiming to steal passwords and inject false information.”
And here’s where it gets spicy: Gawkowski hinted that this attack likely originated from Russia. He described it as part of a broad effort by Russian services to destabilize EU countries ahead of the European Parliament elections.
Currently, the Internal Security Agency and other relevant bodies are preparing a detailed report. Gawkowski emphasized that steps are being taken to ensure PAP is protected against future incidents.
Swift Response and Enhanced Security Measures
Gawkowski highlighted the quick reaction to the attack, stating, “We are entirely safe because within four minutes of the attack, we issued communications identifying it as disinformation. The coordination between the Prime Minister’s Office, the Ministry of Digital Affairs, and the Ministry of the Interior was seamless, with all systems responding effectively.”
He reassured that PAP is now secure and that ongoing checks are in place to prevent any repeat incidents. “We’ve identified and blocked the pathway used to insert the false report into PAP’s service. All technical information necessary to understand this severe incident is being shared with the appropriate authorities. We’re also working on further strengthening our security measures to protect our systems and services.”
The leadership at PAP stated, “We’re committed to close cooperation with the authorities investigating the incident and will continue enhancing our defenses to safeguard against future attacks.”
So, there you have it—a swift and coordinated response has not only neutralized the immediate threat but also set the stage for a more secure future for Poland’s national news agency. Stay tuned, and keep those firewalls up!
